HowTo install NetworkMiner in Ubuntu Fedora and Arch Linux
 NetworkMiner is a network forensics tool primarily developed for Windows OS's, but it actually runs just fine also in other operating systems with help of the Mono Framework.
This guide shows how to install NetworkMiner in three different Linux distros (Ubuntu, Fedora and Arch Linux).
NetworkMiner is a network forensics tool primarily developed for Windows OS's, but it actually runs just fine also in other operating systems with help of the Mono Framework.
This guide shows how to install NetworkMiner in three different Linux distros (Ubuntu, Fedora and Arch Linux).
STEP 1: Install Mono
Ubuntu (also other Debian based distros like Xubuntu and Kali Linux)
sudo apt install mono-devel
CentOS/RHEL
sudo yum install mono-devel
Fedora
sudo dnf install mono-devel
ArchLinux
sudo pacman -S mono
Verify that you have installed Mono version 5 or later with
mono --version
Mono JIT compiler version 5.18.0.240 (Debian 5.18.0.240+dfsg-2ubuntu2 Wed Apr 17 23:39:09 UTC 2019)
Copyright (C) 2002-2014 Novell, Inc, Xamarin Inc and Contributors. www.mono-project.com
TLS: __thread
SIGSEGV: altstack
Notifications: epoll
Architecture: amd64
Disabled: none
Misc: softdebug
Interpreter: yes
LLVM: supported, not enabled.
Suspend: preemptive
GC: sgen (concurrent by default)
The example output above shows Mono 5.18.0.240 is installed, so we're good to go. But if you're stuck on Mono 4.x or wasn't able to install Mono at all from your package manager, then please resort to the "Installing Mono Manually" section below.
Installing Mono Manually
Users of most Linux flavors as well as macOS
can download and install the latest stable release of the Mono Framwork from here:
https://www.mono-project.com/download/stable/
STEP 2: Install NetworkMiner
wget https://www.netresec.com/?download=NetworkMiner -O /tmp/nm.zip
sudo unzip /tmp/nm.zip -d /opt/
cd /opt/NetworkMiner*
sudo chmod +x NetworkMiner.exe
sudo chmod -R go+w AssembledFiles/
sudo chmod -R go+w Captures/
Note: If you still haven't installed Mono 5 and "Installing Mono Manually" wasn't a viable option, then the latest NetworkMiner release is not for you. Please download NetworkMiner 2.4 instead, which works fine also with older versions of Mono. You can find NetworkMiner 2.4 here:https://www.netresec.com/?download=NetworkMiner_2-4
STEP 3: Run NetworkMiner
mono NetworkMiner.exe --noupdatecheck
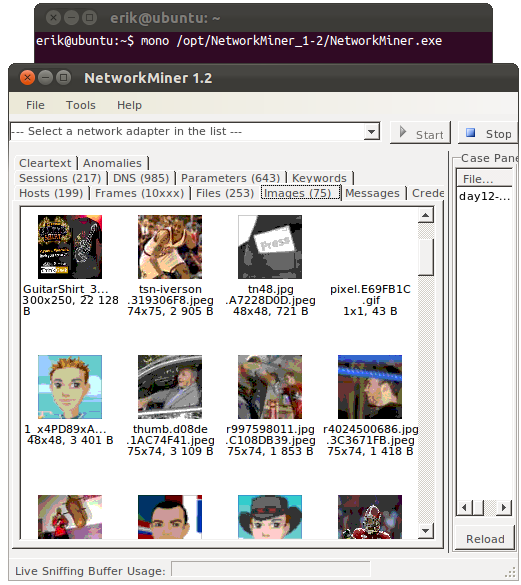
NetworkMiner 1.2 running under Ubuntu Linux, with “day12-1.dmp” from the M57-Patents Scenario loaded.
Live CD's
Another way to try out NetworkMiner in Linux is to spin up a Live DVD or pre-built VM that has the tool installed, such as Security Onion, REMnux, BlackArch or NST.
Live sniffing with NetworkMiner
In order to capture packets (sniff traffic) in Linux you will have to use the “PCAP-over-IP” feature. NetworkMiner is, however, not really designed for packet capturing; it is primarily a tool for parsing and analyzing PCAP files containing previously sniffed traffic.
We recommend using other tools such as tcpdump, dumpcap or netsniff-ng in order to reliably capture packets to a PCAP file. You can read more on how to sniff traffic in our Sniffing Tutorial.
Posted by Erik Hjelmvik on Saturday, 01 February 2014 20:45:00 (UTC/GMT)
Tags: #NetworkMiner #Linux #mono #network forensics



