NetworkMiner Video Tutorials on the Intertubes
There are many good video tutorials for NetworkMiner available on the intertubes, so I thought I would share some of my favorite videos on this blog.
NetworkMiner for Network Forensics
Creator: Adrian Crenshaw (Irongeek)
Publication Date: December 2008
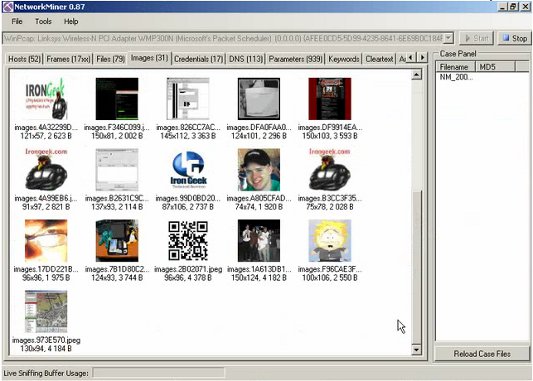
Featuring: NetworkMiner 0.87
Link: http://www.irongeek.com/i.php?page=videos/networkminer-for-network-forensics
Adrian Crenshaw, a.k.a. Irongeek, is a very active guy in the network security field. He was, not surprisingly, also an early adopter of NetworkMiner. Adrian has put together a great tutorial on NetworkMiner, which is best viewed by visiting the Irongeek webpage.
Network Tap Analyzers
Creators: Hak5 and Mubix (Rob Fuller)
Publication Date: May 2009
Featuring: NetworkMiner 0.87 and NetWitness Investigator
Link: http://revision3.com/bestof/hak5-514
Hak5 do some great quality video productions, even though the show hosts (Darren and Shannon) might not always get all the technical details right.
In this episode of Hak5 Mubix joins the show to demo a couple of network forensics tools. Apart from showing how to access reassembled files, credentials and parameters Mubix also extracts the SA credentials for an SQL database from captured network traffic.
Network miner packet analyzer.avi
Creator: martinswfranzen
Publication Date: May 2010
Featuring: Wireshark and NetworkMiner 0.91
Link: http://www.youtube.com/watch?v=nKY14oEkGGw&hd=1
This tutorial unfortunately has no sound, but I still enjoy it. The tutorial shows web traffic being sniffed Wireshark and saved to a pcap file. The pcap is then loaded into NetworkMiner and various reassembled web pages are displayed. The tutorial also shows how credentials (username and password) can be extracted with NetworkMiner for unencrypted logins to the content management system webSPELL.
Twitter Security Hole
Creator: Steven Whiting
Publication Date: May 2010
Featuring: NetworkMiner 0.91
Link: http://www.youtube.com/watch?v=2brI4dy3gdc
Steven shows how he was able to use NetworkMiner to extract his Twitter username and password while changing his account settings. Steven also has another video showing a related security flaw in Twitter.
I alerted security@twitter.com about this flaw on May 5 2010 and got a swift acknowledgment from Bob Lord. It did, however, take Twitter several months until they had mitigated the flaw by applying HTTPS for when users re-enter their passwords on their website.
Network Miner Tutorial
Creator: Anton Schieffer
Publication Date: February 2011
Featuring: NetworkMiner 0.92
Link: http://www.youtube.com/watch?v=7CysHUdkKeY&hd=1
In this tutorial Anton talks about OS fingerprinting and shows how to access extracted files, images and extracted login credentials. Anton also provides a nice example of how to use the keyword search functionality in NetworkMiner.
Creating new NetworkMiner videos
There to this date no video tutorials for NetworkMiner 1.0 published on the Internet. I would be happy to promote such new videos on this blog. It would also be fun to see a video showing how to solve one of the many network forensic challenges available on the Internet, such as the DFRWS 2008 challenge, the Tao Security TCP/IP Weapons School Sample Lab or any of the many puzzles at forensicscontest.com.
Some hints on what to look for in these pcap files can be found in the slides for the Network Forensics Workshop I held at the Europol High Tech Crime Experts Meeting back in 2009.
PS. You can find even more publicly available pcap files at our list of publicly available PCAP files.
UPDATE 2018-02-15
We have released a series of Network Forensics Video Tutorials, which show how NetworkMiner as well as other tools can be used in order to analyze network traffic in PCAP files.
Posted by Erik Hjelmvik on Tuesday, 22 February 2011 17:15:00 (UTC/GMT)
Tags: #NetworkMiner



