HowTo handle PcapNG files
Users of Wireshark 1.8.0 (or later) have most likely noticed that the default output file format has changed from libpcap (.pcap) to Pcap-NG (.pcapng). So what does this mean other than a longer file extension?
New Features in PcapNG
PcapNG is short for “PCAP Next Generation Dump File Format”. This new format isn't just an update of the old PCAP specification, but a total rewrite of the whole spec. Here are a few of the features that are available in the new PcapNG format:
- Traffic captured from multiple interfaces can be stored in a single file. This even works when the interfaces have different data link types, such as Ethernet, 802.11 (WiFi) and PPP.
- PcapNG trace files can be tagged with metadata info about what OS, hardware and sniffer application that was used to capture the traffic. Wireshark and dumpcap automatically tags generated PcapNG files this way.
- There is a long list of metadata attributes that can be stored about each interface. This list includes attributes like interface name, dropped packets and used capture filter.
- Text comments can be added and saved to individual frames. These comments, which are called “annotations”, are available in Wireshark and Tshark via the display filter named “pkt_comment”.
You can, for example, use tshark to list all annotations in a PcapNG file with the following command:
tshark -r dump.pcapng -T fields -e pkt_comment -R pkt_comment
You might also have seen improved timestamp resolution as a new feature of the PcapNG format. It is true that the PcapNG format allows for more precise timestamps compared to the microsecond resolution provided by the old PCAP format. This does, however, not mean that you will get nanosecond resolution in your capture files just because you switch to the PcapNG format. The default timestamp resolution in PcapNG files is still microseconds, and tools like Wireshark and dumpcap additionally only get microsecond resolution timestamps from the library they rely on for packet capturing (i.e. libpcap or WinPcap).
Compatibility Issues
Many tools are not yet able to load PcapNG files, instead they'll spit out error messages like “bad dump file format”.
These error messages typically appear when a tool parses PCAP files with help of a libpcap version
prior to 1.1.0 (you can find the error message in
savefile.c from early 2010).
If you instead load a PcapNG file into NetworkMiner you'll currently get the following error message:
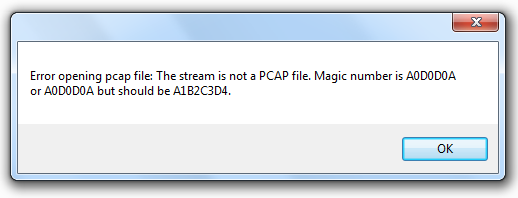
NetworkMiner 1.4.1 with error message while trying to open a PcapNG file
Convert PcapNG to PCAP
If you end up with a capture file in the PcapNG format, which you need to parse with a tool that does not yet support the “NG” format, then you'll have to convert it to the legacy PCAP format.
One way to achieve this is to open the PcapNG file in Wireshark and click “File, Save As...”. Then select the “Wireshark/tcpdump/... - pcap” option in the “Save as type” drop-down list.You can also use editcap to do the conversion like this:
editcap -F pcap dump.pcapng dump.pcapHowever, if the PcapNG file contains traffic from multiple interfaces with different data link types then you'll get an error message saying:
editcap: Can't open or create dump.pcap: That file format doesn't support per-packet encapsulations
One way to convert such multi-encapsulation PcapNG files back to PCAP format is to first split the capture file into multiple PcapNG files, by using the display filters “frame.interface_id” or “frame.dlt”, and then convert each individual PcapNG file back to PCAP using editcap.
Sniff to PCAP
If you want to avoid conversion issues altogether then it's probably safest to stay with the good ol' PCAP format. But since dumpcap defaults to PcapNG nowadays you'll have to tell it to use the legacy PCAP format with the “-P” switch like this:
dumpcap -P -i eth0 -w dump.pcap
Posted by Erik Hjelmvik on Wednesday, 05 December 2012 12:15:00 (UTC/GMT)
Tags: #PcapNG #Pcap-NG #PCAP #convert #editcap #tshark #NetworkMiner #dumpcap



