Enable file extraction from PCAP with NetworkMiner in six steps
NetworkMiner can reassemble files transferred over protocols such as HTTP, FTP, TFTP, SMB, SMB2, SMTP, POP3 and IMAP simply by reading a PCAP file. NetworkMiner stores the extracted files in a directory called “AssembledFiles” inside of the NetworkMiner directory.
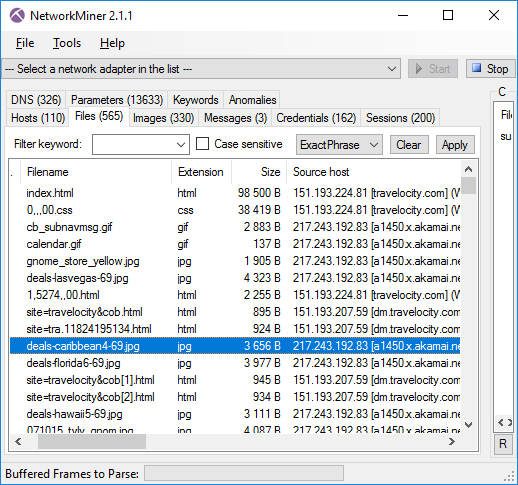
Files extracted by NetworkMiner from the DFRWS 2008 challenge file suspect.pcap
NetworkMiner is a portable tool that is delivered as a zip file. The tool doesn’t require any installation, you simply just extract the zip file to your PC. We don’t provide any official guidance regarding where to place NetworkMiner, users are free to place it wherever they find it most fitting. Some put the tool on the Desktop or in “My Documents” while others prefer to put it in “C:\Program Files”. However, please note that normal users usually don’t have write permissions to sub-directories of %programfiles%, which will prevent NetworkMiner from performing file reassembly.
Unfortunately, previous versions of NetworkMiner didn’t alert the user when it failed to write to the AssembledFiles directory. This means that the tool would silently fail to extract any files from a PCAP file. This behavior has been changed with the release of NetworkMiner 2.1. Now the user gets a windows titled “Insufficient Write Permissions” with a text like this:
User is unauthorized to access the following file:
C:\Program Files\NetworkMiner_2-1-1\AssembledFiles\cache\FILENAME
File(s) will not be extracted!
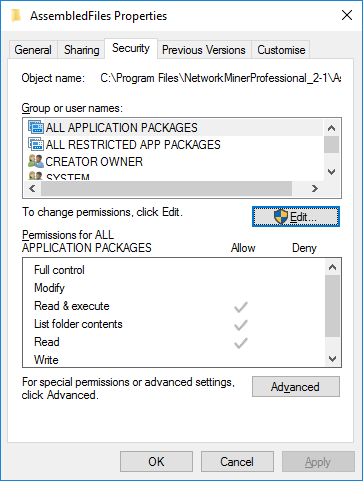
Follow these steps to set adequate write permissions to the AssembledFiles directory in Windows:
- Open the Properties window for the AssembledFiles directory
- Open the “Security” tab
- Press “Edit” to change permissions
- Select the user who will be running NetworkMiner
- Check the “Allow”checkbox for Write permissions
- Press the OK button
If you are running NetworkMiner under macOS (OS X) or Linux, then please make sure to follow our installation instructions, which include this command:
sudo chmod -R go+w AssembledFiles/
Once you have set up the appropriate write permissions you should be able to start NeworkMiner and open a PCAP file in order to have the tool automatically extract files from the captured network traffic.
Posted by Erik Hjelmvik on Friday, 03 March 2017 09:44:00 (UTC/GMT)
Tags: #NetworkMiner #PCAP #NSM



