Remote Sniffing from Mikrotik Routers
One of the new features in NetworkMiner 2.9 is a TZSP streaming server. It is designed to read a real-time stream of sniffed packets from Mikrotik routers. This method for remote sniffing can be used to capture packets regardless if NetworkMiner is running in Windows or Linux.
How to Sniff Packets with TZSP
Open a console or terminal on the Mikrotik router and run “/tool sniffer print” to see the current settings. Then run the following commands to configure the sniffer:
- /tool sniffer
- set streaming-enabled=yes
- set streaming-server=10.1.2.3:37008
- set filter-stream=yes
Replace 10.1.2.3 with the IP address of the computer running NetworkMiner
It is also possible to activate the sniffer from the RouterOS WebFig interface.
- Expand the “Tools” section
- Click “Packet Sniffer”
- Check “Streaming Enabled”
- Enter IP of computer running NetworkMiner in Server
- Enter 37008 as Port
- Check “Filter Stream”
- Click the “Apply” button at the top
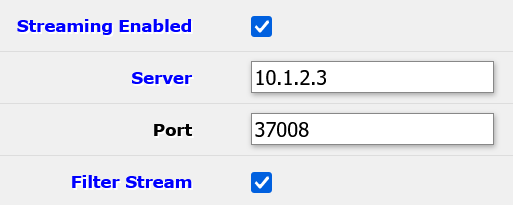
The “filter-stream” setting prevents the sniffer from capturing packets that are sent to the streaming-server (i.e. NetworkMiner). This setting must be enabled to avoid a snowball effect, where copies of previously captured packets get sniffed and re-transmitted to the streaming-server.
The next step is to open the TZSP window in NetworkMiner, which you’ll find under “File, Receive TZSP Stream”.
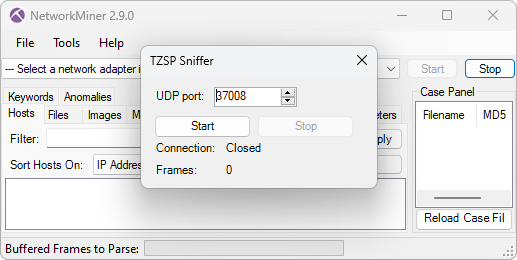
Click “Start” in NetworkMiner’s TZSP window, so that it listens for an incoming TZSP stream on UDP port 57008. Go back to the Mikrotik router, where you start the sniffer with “/tool sniffer start” or by clicking the “Start” button in the WebFig. You should now see the Frames counter increasing in NetworkMiner's TZSP window. You’ll probably also notice that artifacts get added to the main NetworkMiner window in the background as more packets are received.
Close the sniffer by running “/tool sniffer stop” or clicking the “Stop” button in WebFig, then click “Stop” in NetworkMiner. You can now close NetworkMiner’s TZSP window to view the artifacts that NeworkMiner has extracted from the captured traffic.
Posted by Erik Hjelmvik on Thursday, 30 May 2024 13:05:00 (UTC/GMT)
Tags: #TZSP #NetworkMiner #sniffer



