Remcos Alerts from FlowCarp in EveBox
There is a wonderful little web-based alert and event front-end called EveBox, which renders Eve JSON formatted data to a web UI. This blog post demonstrates how EveBox can be used to show alert and flow information that FlowCarp has extracted from a Remcos malware infection.
Remcos RAT
The starting point of my analysis will be a PCAP file with network traffic from a Remcos RAT infection, which Brad Duncan has published on Malware-Traffic-Analysis.net. The password scheme for the zip file containing the PCAP can be found here, in case you'd like to follow along and perform the same analysis steps yourself. All commands and examples in this blog post can be run in both Linux and Windows.
JSON formatted alerts and flow data can be extracted from the PCAP file with FlowCarp like this:
But the free community license of FlowCarp doesn't include a protocol model for Remcos, which is why this command will generate flow events but no alerts about detected Remcos malware traffic. I will therefore submit the pcap file to the free FlowCarp demo server instead, which has a commercial license that can identify over 600 protocols. No registration or API key is required to use this demo server (as long as users behave − please behave).
The downloaded remcos-eve.json file uses the Suricata Eve JSON format, so jq queries typically used to process Suricata eve.json log files can be used to parse and filter the JSON output from FlowCarp as well.
- jq -c 'select(.event_type=="alert")|[.dest_ip, .dest_port, .proto, .alert.signature]' < remcos-eve.json
- ["193.178.170.155",443,"TCP","MALWARE protocol detected: TLS, Remcos"]
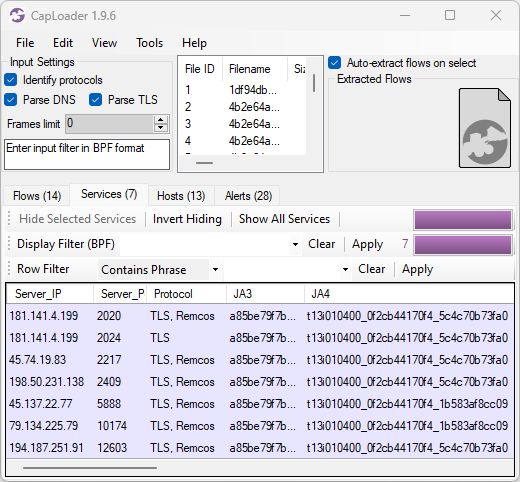
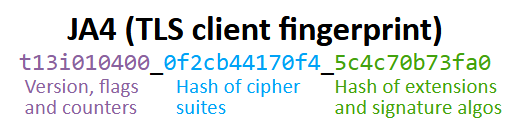
This FlowCarp alert indicates that the PCAP file contains TLS-encrypted Remcos traffic, which means that FlowCarp has performed a so-called sub-protocol match to detect the protocol inside of TLS without decrypting the TLS layer. A quick way to verify if this traffic is Remcos in TLS is to check the JA3 hash or JA4 fingerprint of the client's TLS handshake.
- tshark -r 2026-03-12-SmartApeSG-ClickFix-activity-for-Remcos-RAT.pcap -Y "ip.dst == 193.178.170.155 and tls.handshake" -T fields -e tls.handshake.ja3 -e tls.handshake.ja4
- a85be79f7b569f1df5e6087b69deb493 t13i010400_0f2cb44170f4_5c4c70b73fa0
This nicely matches what we expect to see from TLS encrypted Remcos traffic. For reference these are the JA3 and JA4 fingerprints typically associated with Remcos:
- JA3: a85be79f7b569f1df5e6087b69deb493
- JA4: t13i010400_0f2cb44170f4_5c4c70b73fa0
- JA4: t13i010400_0f2cb44170f4_1b583af8cc09
There is always a risk of false positives associated with JA3 or JA4 fingerprints, so a rule of thumb is to not blindly trust JA3/JA4 based alerts without having additional indicators of compromise. FlowCarp performs a much deeper identification of sub-TLS protocols than JA3/JA4, but there's still a false positive risk associated with detection of encrypted malware traffic — so make sure to verify alerts like this with other types of data sources, such as event logs from the infected device or OSINT information about the suspected C2 server. For this alert we can see that @DonPasci has reported 193.178.170.155:443 to ThreatFox as being a Remcos C2 server.
EveBox
EveBox is a web-based front-end for Suricata "EVE" alerts and events, created by Jason Ish. The EveBox source code lives on GitHub and pre-built EveBox binaries for Linux and Windows are available on evebox.org.
This evebox command will fire up a browser and render information about the flows and alerts in the Eve JSON file from FlowCarp:
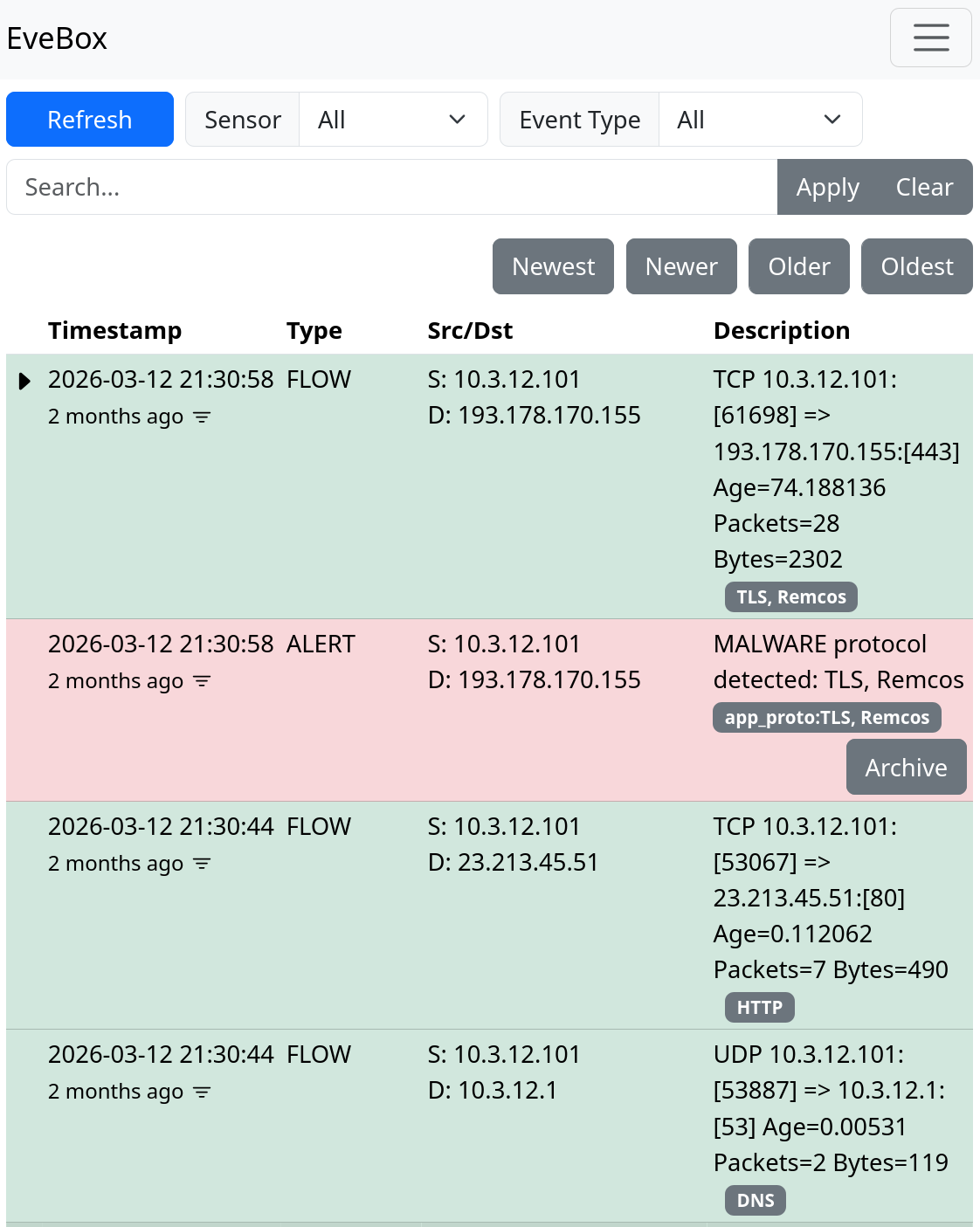
The flows and alerts are displayed in reverse order, so that the most recent events are on top. The Remcos alert stands out in red and immediately catches your eye. Let's change Event Type from "All" to "Alert" just to make sure there are no other alerts.
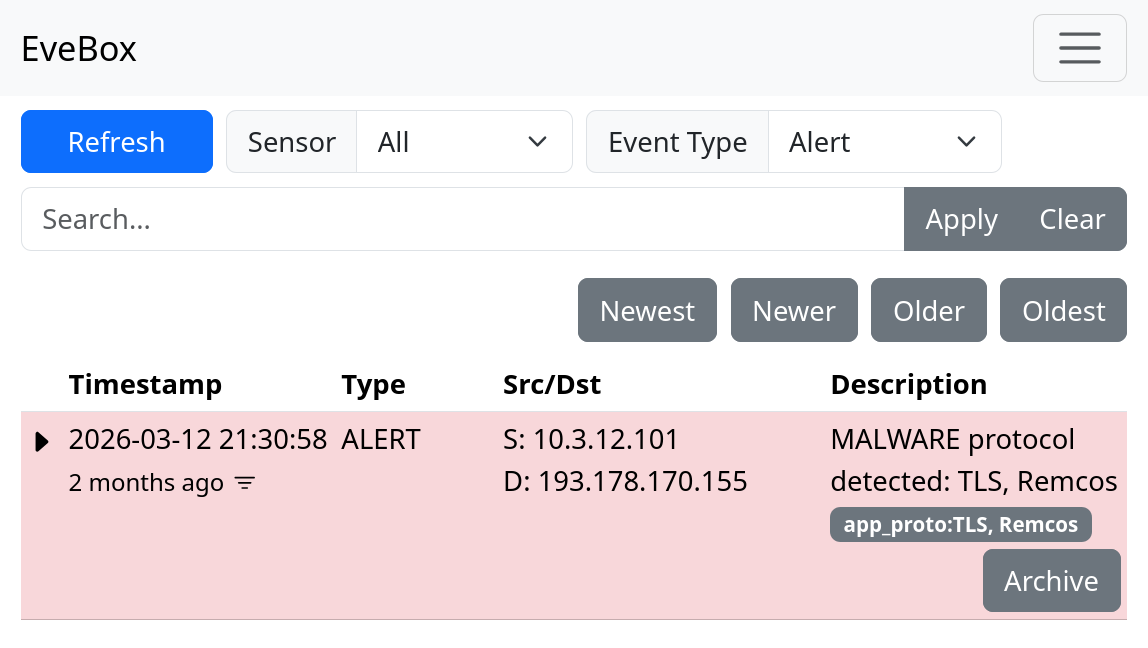
Looks like this was the only alert in this JSON file.
EveBox is built for Suricata, but it's really nice that it can be used out-of-the-box to read FlowCarp's JSON logs as well. For reference, let's also see what it looks like when we run the same PCAP file through Suricata and import eve.json into EveBox.
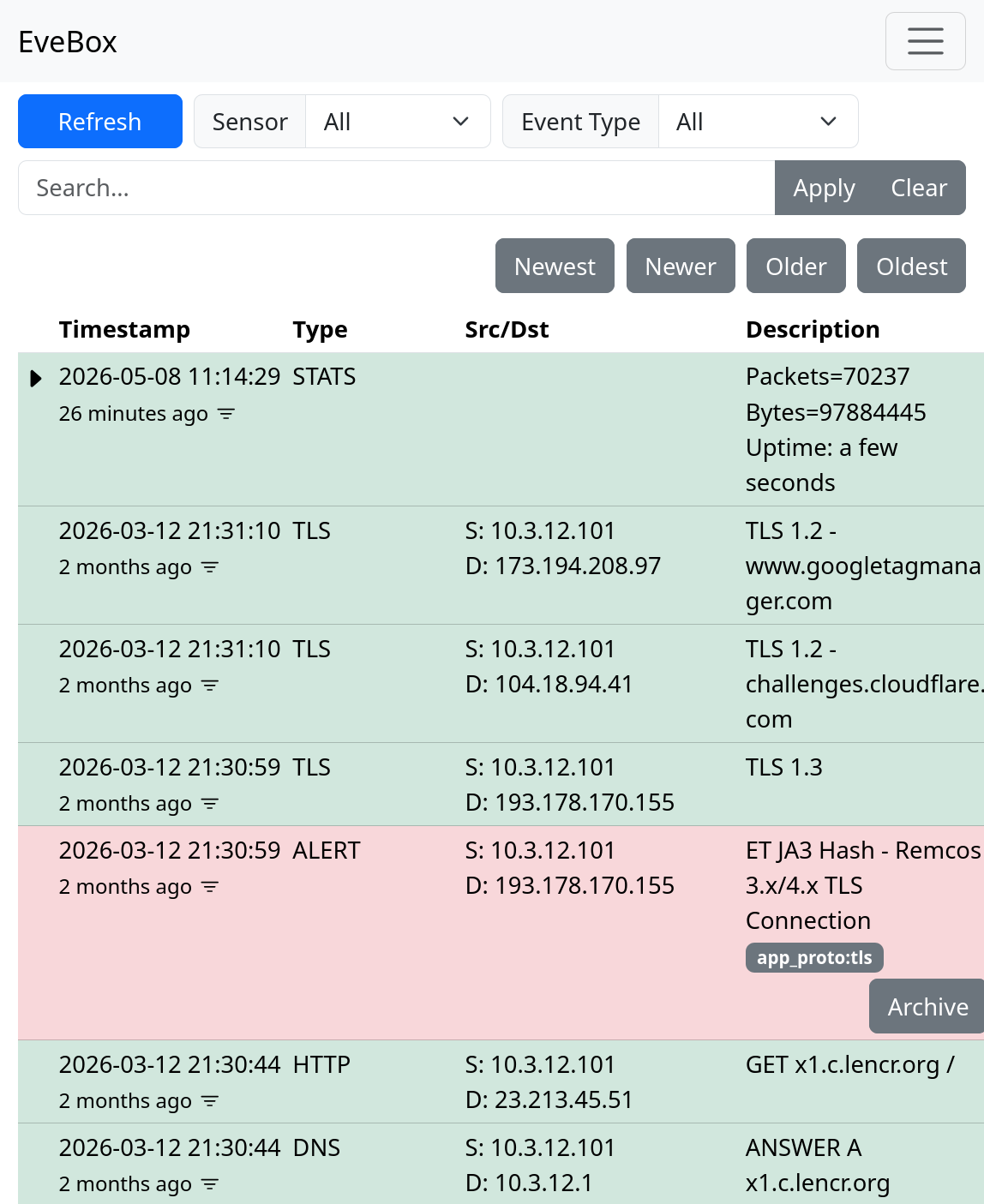
I'm happy to see that Suricata also alerts on the same TCP session as FlowCarp. This alert was raised by the Emerging Threats signature ID 2036594, which triggers whenever the JA3 hash of a TLS handshake is a85be79f7b569f1df5e6087b69deb493.
Posted by Erik Hjelmvik on Friday, 08 May 2026 11:49:00 (UTC/GMT)
Tags: #FlowCarp #Remcos #a85be79f7b569f1df5e6087b69deb493 #t13i010400_0f2cb44170f4_5c4c70b73fa0 #t13i010400_0f2cb44170f4_1b583af8cc09