Hunting for C2 Traffic
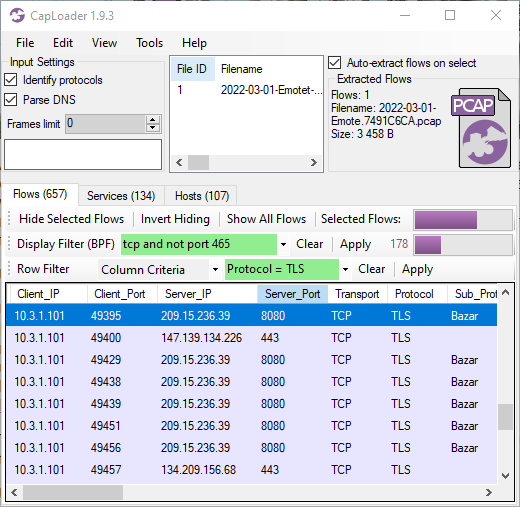
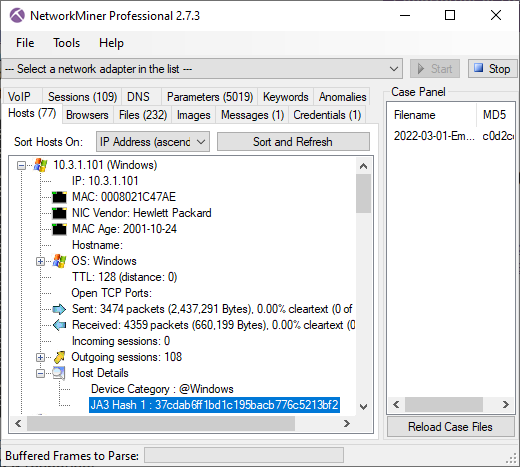
In this video I look for C2 traffic by doing something I call Rinse-Repeat Threat Hunting, which is a method for removing "normal" traffic in order to look closer at what isn't normal.
The video was recorded in a Windows Sandbox in order to avoid accidentally infecting my Windows PC with malware.
The PCAP files analyzed in the video are:
- 2022-06-27-part-1-of-2-Qakbot-with-Cobalt-Strike-and-DarkVNC.pcap
- 2022-06-27-part-2-of-2-Qakbot-with-DarkVNC-and-email-banner-traffic.pcap
- 2022-06-28-TA578-IcedID-with-Cobalt-Strike-raw.pcap
Thank you for sharing these capture files Brad!
IOC List
- QBot source: 23.29.125.210
- QBot md5: 2b55988c0d236edd5ea1a631ccd37b76
- QBot sha1: 033a22c3bb2b0dd1677973e1ae6280e5466e771c
- QBot sha256: 2d68755335776e3de28fcd1757b7dcc07688b31c37205ce2324d92c2f419c6f0
- Qbot proxy protocol server: 23.111.114.52:65400
- QBot C2: 45.46.53.140:2222
- QBot C2 JA3: 51c64c77e60f3980eea90869b68c58a8
- QBot C2 JA3S : 7c02dbae662670040c7af9bd15fb7e2f
- QBot X.509 domain: thdoot.info
- QBot X.509 thumbprint: 5a8ee4be30bd5da709385940a1a6e386e66c20b6
- IcedID BackConnect server: 78.31.67.7:443
- IcedID BackConnect server: 91.238.50.80:8080
References and Links
- herALook.dat (MalwareBazaar)
- herALook.dat (VirusTotal)
- Qbot proxy protocol details (Securelist)
- QBot JA3 hash (DFIR Report)
- IcedID BackConnect protocol (Group-IB)
Update 2022-10-13
Part two of this analysis has been published: IcedID BackConnect Protocol
Posted by Erik Hjelmvik on Friday, 30 September 2022 12:37:00 (UTC/GMT)
Tags: #Threat Hunting #PCAP #CapLoader #NetworkMiner #NetworkMiner Professional #Video #QBot #QakBot #51c64c77e60f3980eea90869b68c58a8 #IcedID #TA578