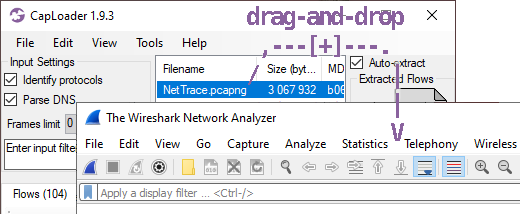
How to set PCAP as default save file format in Wireshark
Did you know that there is a setting in Wireshark for changing the default save file format from pcapng to pcap?
In Wireshark, click Edit, Preferences. Then select Advanced and look for the
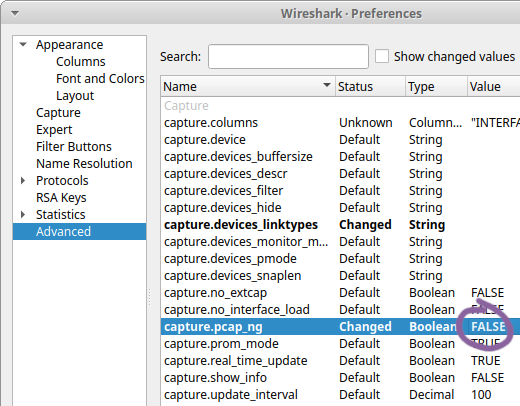
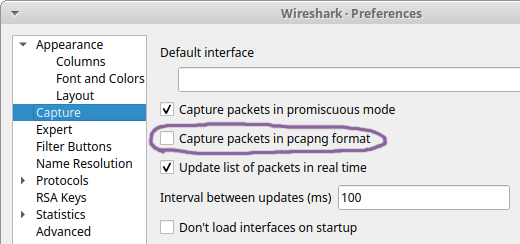
This setting can also be accessed from the Capture tab in Preferences.
I recently learned about this setting from Sake Blok when he commented on my feature request to have Wireshark use pcap as default savefile format instead of pcapng. I have a feeling that this feature request will not be accepted though, since it has received several downvotes. That’s why I’m trying to spread the word about this setting instead, so that everyone who prefers the pcap file format over pcapng can change the default behavior in their own Wireshark installation.
This setting doesn’t affect command line tools, like dumpcap, tshark, mergecap etc. So if you want to capture packets with dumpcap to a pcap file then you need to use the
Other command line tools in the Wireshark suite, like tshark and mergecap, require that you instead specify
What’s Wrong with PCAP-NG?
Why all this fuss about using PCAP instead of PCAP-NG? Well, it turns out that most Wireshark users are happily unaware of just how much metadata there is in the pcapng files they share online. This metadata typically contains information about the CPU of their computer, the exact version and build of their operating system as well as the name of the network interface on which the capture was performed. For Windows users the network interface details even contain a GUID that usually is a world-unique identifier.
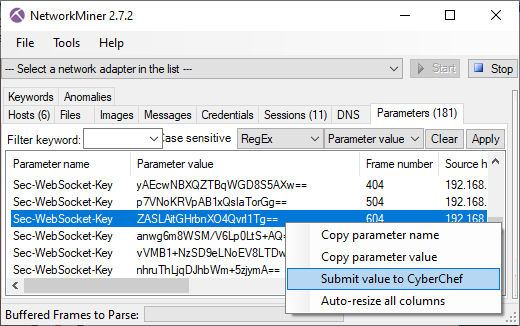
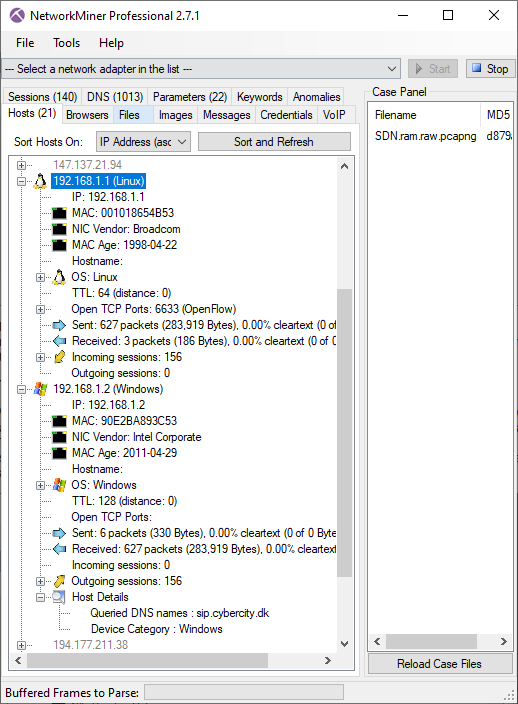
I was once even able to identify a person, who had anonymously shared a pcapng file online, by inspecting metadata in the shared capture file github.pcapng. Here's the metadata in that capture file:
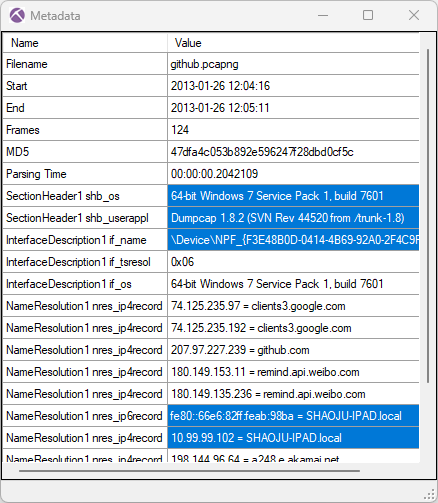
This screenshot shows the output from the “Show Metadata” functionality in NetworkMiner Professional. There's also a great way to show pcapng metadata in Wireshark: Open the pcapng file, click View, Reload as File Format/Capture (Ctrl+Shift+F).
Mergecap
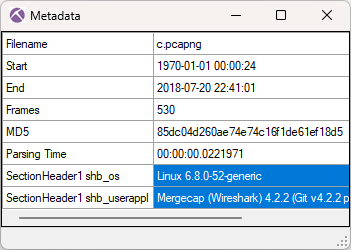
The previously mentioned command line tool mergecap, which joins multiple capture files into one, outputs pcapng files by default. In fact, if it is tasked to merge two pcap files (having no metadata), it then creates a pcapng file containing the packets from the two input pcap files enriched with metadata about the computer running mergecap. This metadata is typically information about the operating system as well as the version of mergecap that was used.
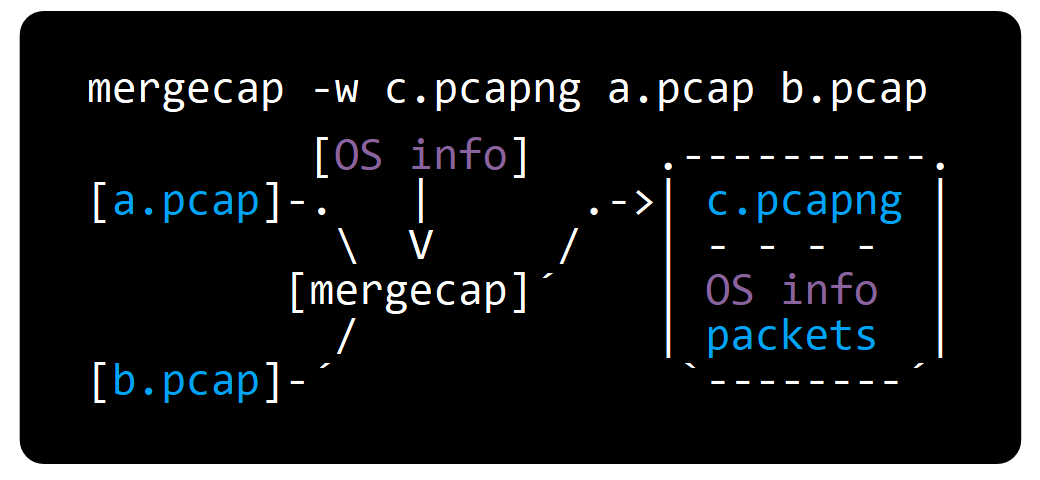
Providing an output file with the “.pcap” suffix to mergecap will not help, mergecap still generates a pcapng file. You have to use the
What do Wireshark Users Want?
I recently conducted two unscientific polls, where I asked which savefile format Wireshark should use as default.
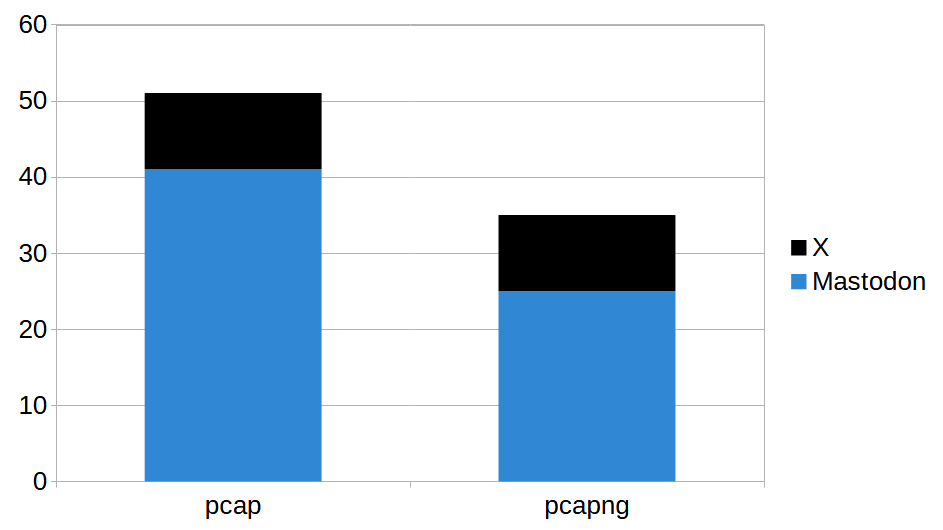
In total the polls got 86 votes, where 51 voted for pcap and 35 preferred pcapng. I don't want to draw any real conclusions from these results though, primarily due to the low number of participants but also because there might be a bias among the people who were reached by these polls.
Looking Ahead
I reach out to people I know every now and then when I notice that they are sharing pcapng files containing potentially sensitive metadata. They then have to decide if they are okay with this or if they want to go through the process of replacing the pcapng files with pcap files. In many cases they choose the latter, which can be quite tricky if that involves removing files from GitHub.
I eventually got tired of doing this, especially when I realized that even very skilled Wireshark users often don’t know that pcapng files store metadata about their computers. Reminding people to select the “pcap” format every time they save a capture file doesn’t seem to be the solution. I therefore hope that this blog post can help Wireshark users avoid accidentally sharing unnecessary metadata in the future.
For more information about the pcapng format, please visit pcapng.com.
Update 2025-02-26
I have now created two new feature requests for Wireshark. The first request is to add settings in Wireshark that allow users to control what metadata that get saved to pcapng files. The other one is to have Wireshark select output file format based on filename suffix instead of always creating a pcapng file.
Posted by Erik Hjelmvik on Tuesday, 25 February 2025 10:33:00 (UTC/GMT)
Tags: #wireshark #PCAP #pcap-ng #dumpcap #metadata #ASCII-art